| Back |
ebaY Insider Hijack Scam?
|
|

ebaY Insider Hijack
Scam
Sat 16 Dec 06
Part I Update
Updated 28 Dec Part II
Part II Update
On Tuesday 12 Dec 2006 we received an email from a subscriber, describing how
his ebaY selling account had been hijacked, and was being used to sell BAPE Hoody
shirts. There were many interesting elements of this hijacking, different from
those we have seen in the past. Upon seeing items he had not listed, the legitimate
account holder, let's call him Jack, removed the listings and changed his password
on the account. In addition he found that all his email notification preferences
had been set to NO. He set them back to YES. By lunch time, the fake items were
back, so this time using a work computer, Jack changed his ebaY password again.
This made no difference and the items reappeared.
Jack's home computer is firewalled and has a full complement of detection software
installed and active. He is a savvy user well versed in phishing, and has not
responded in a long time to any ebaY "second chance" offers. He has not logged
in to ebaY via any channel but his own links, and he has not filled in any pop
up sign in request. Jack's work computer is on a very secure system, as he works
in an industry where online security is paramount. He did not fall for a scam,
have his computer invaded, have his identity stolen or compromised.
In trying to analyze what was going on, it appeared that the hijacker or hijackers
had to have access to accounts independent of passwords, and have the ability
to set account parameters so the legit account holder would not know what was
going on. If this is so, it either points to someone working inside ebaY, or
to a security hole so big, you can drive a tractor trailer through it. Neither
situation is tolerable.
Searching ebaY for BAPE Hoody, brought up 140 pages of one day listings. All
the one day listings were on hijacked accounts, and the hijacked accounts were
used in groups by the first letter, so accounts with very high (usually 100%)
feedback, starting with the letters G, H, I, J were in great evidence. The accounts
were US accounts, but in reading the description, certain phrases would indicate
that English was not the scammers first language. A check of the feedback would
show the legitimate account holder as being a buyer only, or a seller of items
not including designer clothing, or any clothing for that matter. Many accounts
had been inactive for many months or years.
We did a buy it now on one item that was evidently on a hijacked account. We
pulled the account holder's contact info, and it all appeared legitimate via
a white pages check. We checked their email address against their PayPal address
on PayPal, and that too appeared legitimate. The scammer never contacted us for
payment, so we don't know how that part of the scam would have worked. Other
emails with questions sent to the scammers by the folks helping us with this
investigation, yielded answers such as "yes, if you buy two items ,you only pay
them with 150USD .thanks" and "to you address total pay only US160.00" again
suggesting that English was not their first language, and that the scammer had
access to emails sent through the ebaY system. We tried another two BINs, but
never heard from the scammer, despite repeated requests for payment information.
The net result is, we don't know how the scammer worked this so that they received
the payment rather than the legitimate account holder. We did eventually receive
an email from the legitimate account holder on the last two BINs we did, saying
their account was hijacked and not to make payment.
Part I Update
UPDATE 4 Jan 06- After following several of these listings and doing several "buys",
the folks helping TAG with this found that the way the scammers have been getting
paid is to insert their own email address for payment through PayPal. When a
buyer clicks on Buy It Now (which is how most of these listings are set up) they
get taken to a page where they can do an immediate payment through PayPal. When
they do make payment in this manner, the email address the payment gets sent
to is that of the scammer selling these counterfeit goods, not the legitimate
account owner. Once paid for the buyer IS receiving the merchandise in many cases.
It is counterfeit merchandise, not authentic, made in China based on the patterns
of the originals, stolen by the counterfeiter and probably sanctioned by the
Chinese government. Further research is showing that many of these scammers were
legitimate sellers on ebaY in the past, but since ebaY no longer permits sellers
from China to sell this merchandise on ebaY, they are working around the prohibition
by using hijacked accounts.
These items continued to be listed every day, with ebaY only shutting down a
small percentage of them. If this is an ebaY insider job, TAG is baffled as to
why they haven't tracked this to the source and shut it down.
As a matter of interest, some of the images have been tracked to this source
whose domain is registered in Beijing, China -
http://www.xhxh246.com/Product.asp?BigClassName=BAPESTASHOES
http://www.xhxh246.com/index.asp
This story is ongoing, so we will update it as we find more information.
Part II
************************************************************
EBAY'S BACK DOOR WIDE OPEN & LETTING SCAMMERS IN
************************************************************
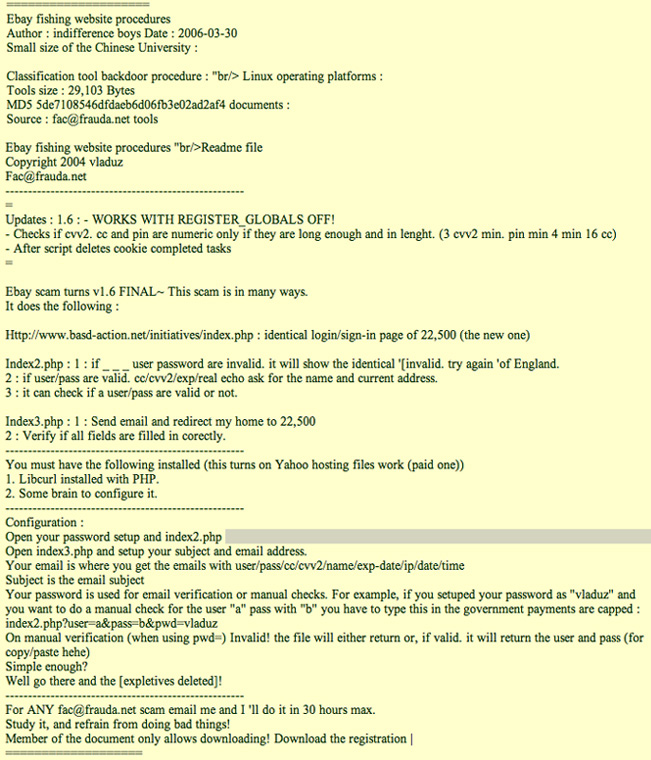
There is a scammer's tool floating around the web that has been offered for sale
to several ebaY users. This tool allows a scammer to access ALL user info through
a utility ebaY uses to track all user information.
If you look at this link, you will see a page with ebaY seller information overlaid
with the scammers SCO Helper program that allows the scammer to send second chance
offers through ebaY's own system, to potential victims who have bid on the legitimate
seller's items.
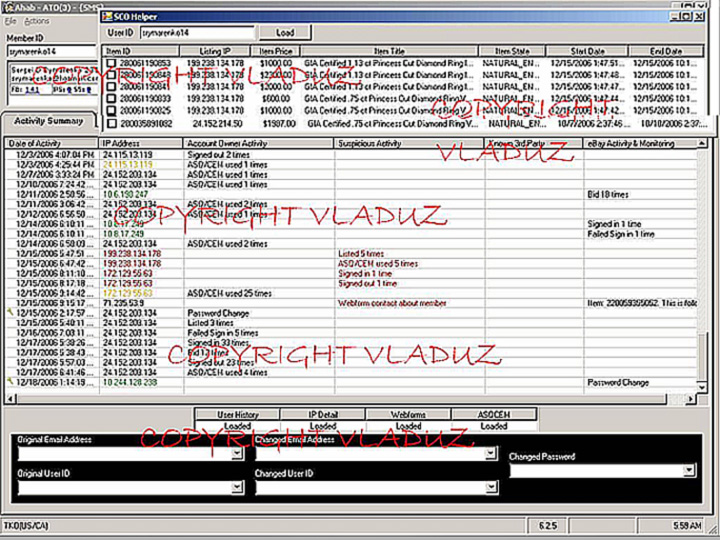
Vladuz
appears to be the person who wrote the program to break
into the part of ebaY where all user information resides,
and where it can be manipulated. He/She also appears
to have authored "utilities" to
exploit this open back door - such as the SCO Helper,
that allows scammers to exploit second chance offers.
As far as we can figure from online research, Vladuz
is the online handle of a Romanian programmer/hacker,
whose name pops up in relation to various scammer sites.
It is very possible that this ebaY function is what is being used by the scammers
to post the BAPE auctions, and monitor email queries, replies and payments so
they can reroute them. It is obvious that this information is readily accessible
to the scammers, and that ebaY has not done anything to close the back door being
used by the scammers.
For everyone wondering how scammers on ebaY manage to hijack accounts at will,
this is the answer. ebaY says the scammers are getting the info due to ebaY users
falling for phishing scams. That explanation let ebaY off the hook, but TAG never
believed it, as it never made sense. In light of the BAPE scams - see this article
-
BAPE Scam
it was definitely NOT falling for a phishing scam that exposed the user information
of "Jack" or other tech savvy users who have contacted us since, with the same
story. In the article we said that it appeared to have to be an insider with
access to inside ebaY information. We now conclude that it may not be an ebaY
insider, but instead an outsider, with complete access to all user account inside
information.
If this is as it appears, ebaY is and has been aware of this wide open back door,
and can't or won't do anything about it. We will update this on our website as
more information becomes available.
Class action suit anyone?
An interesting note, is that since the earthquake on 26 Dec in Asia, cut off
internet access to China and other Asian countries, the number of scams on ebaY
has dropped drastically, as is easy to see by searching for BAPE Hoody listings.
Another note of interest is a reference to this tool that appeared on a Chinese
Blog. The translation is done via the Google page translator, and as such is
not the greatest - but it gives a good idea of what is going on. We have edited
out a vulgar word or two - but the rest is as it appeared. Please take note of
the dates!
Part II Update
UPDATED 4 Jan 06
A source that is allegedly getting inside ebaY information
says that ebaY is claiming that no such back door access
exists, and that the Vladuz page is just a screenshot of
ebaY's backend that Vladuz managed to get somehow. They
said that everything on the Vladuz page was ebaY's and
that the SCO (second chance offer) tool shown on that page
was theirs also. Of course this does not provide any explanation
for how the scammers have complete access to all information
on ebaY, how they are able to access as many accounts as
they like, and pick and choose the ones they want to exploit.
They don't explain how the scammers can add information
to active listings that belong to a legitimate seller whilst
the listing is in progress, or replace their email address
in the PayPal payment information - ALL without having
the seller's account password.
*****************************************************************

